
Following these steps will prepare your business to perform your own vendor audit.
Quick note: Here we’re using the term vendor audit to include both vendor risk assessment and vendor compliance audits. Depending on the scope of your organization, you may split these into separate but related audit processes.
1. Vet your vendors properly by identifying their worker classifications
As you begin the process, you’ll need to make sure you’ve properly classified all vendors. Are they true third-party vendors, or are some individuals who may be independent contractors or qualify as an employee?
Sorting out which workers fall under which classifications is a thorny subject in many compliance audits, so make sure you vet vendors on the front end.
2. Take meticulous notes and records for vendor management
Bringing on your first vendor can feel like a big step, but it isn’t necessarily all that much to manage. But every time you add another vendor, your vendor risk grows, as does the complexity of your vendor management.
In your initial vendor meetings (onboarding and orientation) and any check-in meetings along the way, make sure to take very careful notes and keep clean records so that you’ll always be able to find the information you need on any vendor you work with.
By the way, you might notice a theme running through the vendor audit process: meetings.
You’ll conduct numerous meetings throughout the process — with vendors and your internal team alike.
Do you wish your meetings were more effective than your current status quo? We’d love to help.
Our meeting ground rules for team meetings is a great place to start.
3. Run a vendor risk assessment carefully and thoroughly
As we discussed earlier, every vendor relationship opens up your business to numerous risks. Ensuring you’re minimizing risk and maximizing value is vital to working with vendors in this modern landscape.
Completing a vendor risk assessment is a complex process all its own, requiring participation from numerous departments in your organization to establish standards for assessing vendor risk. You’re not all alone in creating these standards, though. Service level agreements (SLAs), contracts, and even regulatory requirements help define a framework for this process.
4. Use the right tools to track vendor compliance
Key to any vendor compliance program is tracking whether vendors are actually complying with their contracts, SLAs, and regulatory requirements. Using the right digital tools, then, is essential for any vendor or supplier audit effort.
Your management team and other stakeholders must work together to determine the metrics to track.
Once that’s done, it’s time to start performing that tracking. Vendor questionnaires and vendor meetings (on-site or virtual) can be a part of vendor compliance tracking. Also, quality management systems or vendor audit management tools exist that can enhance your capabilities in this arena.
5. Perform a vendor compliance audit
Tracking vendor compliance in an ongoing way is important, but so is going deeper from time to time by completing a formal vendor compliance audit.
Generally speaking, a vendor compliance audit evaluates whether or how well a vendor is meeting its compliance obligations (typically defined in contracts, SLAs, etc.).
Document these audits extensively because you may need that information later if your organization undergoes an audit. Remember, your business bears the risk when a vendor is out of compliance.
6. Track and monitor the vendor audit process and make improvements along the way
Last, realize that the vendor audit process is iterative and ongoing. No organization gets the process 100% correct on the first attempt — and even if you could, the definition of “100% correct” changes over time as regulations and technology evolve.
Where you identify unnecessary risk or noncompliance, take action with those vendors and schedule follow-ups to ensure vendors have made the necessary adjustments.
And where you notice your own processes failing to deliver results, be willing to make improvements to those processes.
Potential risks to think of when conducting a vendor audit
Why bother with a vendor audit in the first place?
Simple: Vendors create risk.
Every time you connect your systems with a vendor, you open yourself up to risk. Very often, the risk is worth the results — but it pays to be aware of the risks ahead of time.
Watch out for these six risk vectors and, where possible, have a plan in place to mitigate these risks.
1. Cybersecurity risks
Any data that goes out to a vendor is now subject to their security infrastructure, not just yours. If the vendor suffers a breach, your data could be the prize.
2. Operational risks
This broad category includes supply chain, procurement, workflows, service, access to systems, and anything else affecting your day-to-day business.
Let’s say you’ve decided to work with a managed services provider (MSP) to handle your IT help desk needs. On paper, this move will save money, improve efficiency, etc.
You do your technological due diligence and select an MSP that seems like a good fit. But weeks into the (year-long minimum) contract, you start to notice some issues.
Your business efficiency and employee morale start to drop because your team members can’t get reasonable responses from your IT partner. Eventually, you’ll notice productivity or quality dropping — an operational risk incurred by choosing the wrong vendor.
3. Compliance risks
If you’re in an industry with compliance concerns, your vendors could put you at compliance risk. Take HIPAA for example. If HIPAA matters to you, you’re probably already ensuring all vendors are HIPAA compliant. Regardless of a vendor’s compliance and certifications, a vendor's mistake or neglect could negatively affect your business.
A breach of potentially identifiable information (PII) at the call center isn’t all that different from a breach at the hospital or doctor’s office itself, making it a significant third-party risk.
4. Reputational risks
Working with vendors automatically puts your reputation on the line, even for problems you aren’t responsible for and can’t control. That’s because the actions (or inaction) of a vendor you’re working with can create reputational risk — not just for them, but for you.
Here’s an example: Remember that massive, unprecedented cyberattack against Fazio Mechanical Services?
Of course not, right? Unless you’re a cybersecurity wizard, you’d have no reason to know about an insignificant HVAC contractor.
What if, instead, we’d asked, “Remember that massive, unprecedented Target data breach that exposed details on millions of customers?”
Whether you remember it or not, the point remains: Yes, Fazio incurred reputational damage. But millions of Target customers don’t care about Fazio; they care that Target compromised their data.
5. Financial risks
Every risk we’ve evaluated so far leads to additional financial risks. Any realized threat to cybersecurity, operations, compliance, or reputation has financial implications: Lost productivity, lost reputation and customer trust, and even lost certification will disrupt your revenue stream and create financial risk.
Use this Vendor Audit Meeting Template from Vanta
What does one of the most well-known data security companies suggest for vendor audits?
The CEO of Vanta provided this meeting template to help you go over the risks.
Here's her suggested agenda:
Annual Vendor Audit Meeting Agenda
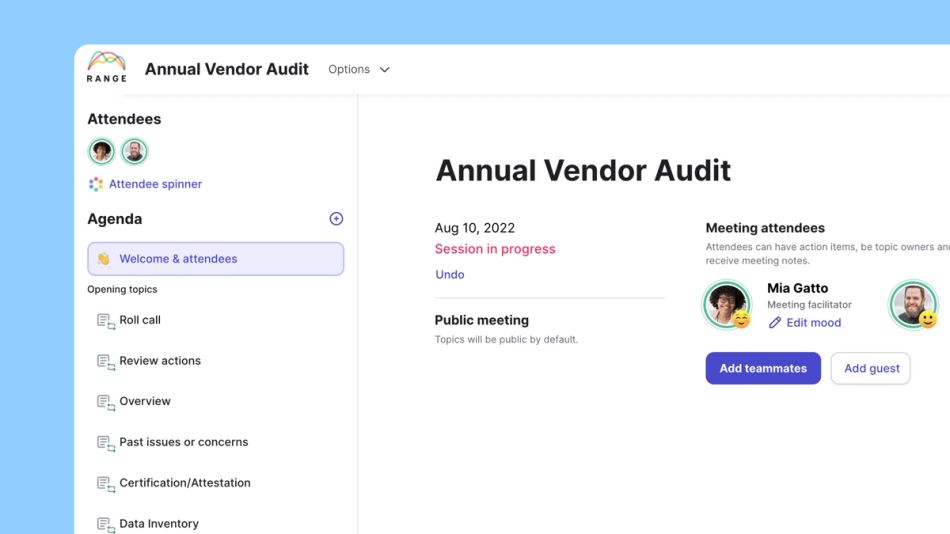
1. Roll call / Check-in
Make note of the vendor you are assessing and who is attending the meeting.
2. Review actions
Review and resolve any actions from the last audit.
3. Overview
- Has anything changed with how we use this vendor?
- Has anything changed with how this vendor provides services?
- Has the service been acceptable?
- Have SLAs been maintained?
4. Past issues or concerns
Were there any issues with the vendor, for example SLA violations, breaches, incidents, etc.
Add topics to the agenda for deeper discussion.
5. Certification/Attestation
Gather evidence of SOC2, ISO27001, PCI AOC, HIPPAA, etc.
- Are they current?
- Do they cover the products and services we use?
- Are there exceptions or qualifications in the report?
6. Data Inventory
What data is the vendor storing and/or processing?
- What is their retention policy?
- Does retention meet our requirements?
- Can we manually request deletion?
7. Security questionnaire
Review responses to any security questionnaires we sent, determine if any follow up actions need to be taken.
8. Assessments
Review the Vendor Risk Assessment, Privacy Impact Assessment (PIA), Transfer Impact Assessment (TIA), if applicable.
9. Regulations
Are we/they compliant with regulations? (GDPR, CCPA, HIPAA, etc.)
10. Contracts
Do we have current contracts with appropriate language? (i.e. BAA/DPA/SCC)
11. Determination
- Are we comfortable with any risks to our business from this vendor?
- Are we comfortable with any risks to Data Subjects from this vendor?
- Do we need to make any changes or implement additional controls?
Sign up for Range for free and invite your team members for more effective meetings.
Vendor Audit FAQ
What is a vendor audit?
What is a vendor audit?
A vendor audit is a process in which an organization evaluates one or more elements of a third-party individual or organization that it has hired to perform a service. Vendor audits are often used to ensure appropriate outcomes, limit risks to the client organization, and validate compliance efforts.
Both vendor risk assessments and vendor compliance audits fall within the broader category of the vendor audit. The former evaluates numerous potential risk sources, including data exposure and cybersecurity threats, while the latter evaluates the vendor’s compliance efforts (with a contract, SLA, or regulatory requirements).








