Range supports single sign on through the Open ID Connect standard. If you would like to configure Okta for your Range workspace, please follow the following steps:
1. Choose the Applications tab from the top level menu of your Okta admin dashboard.
2. Find the button that says Create new app.
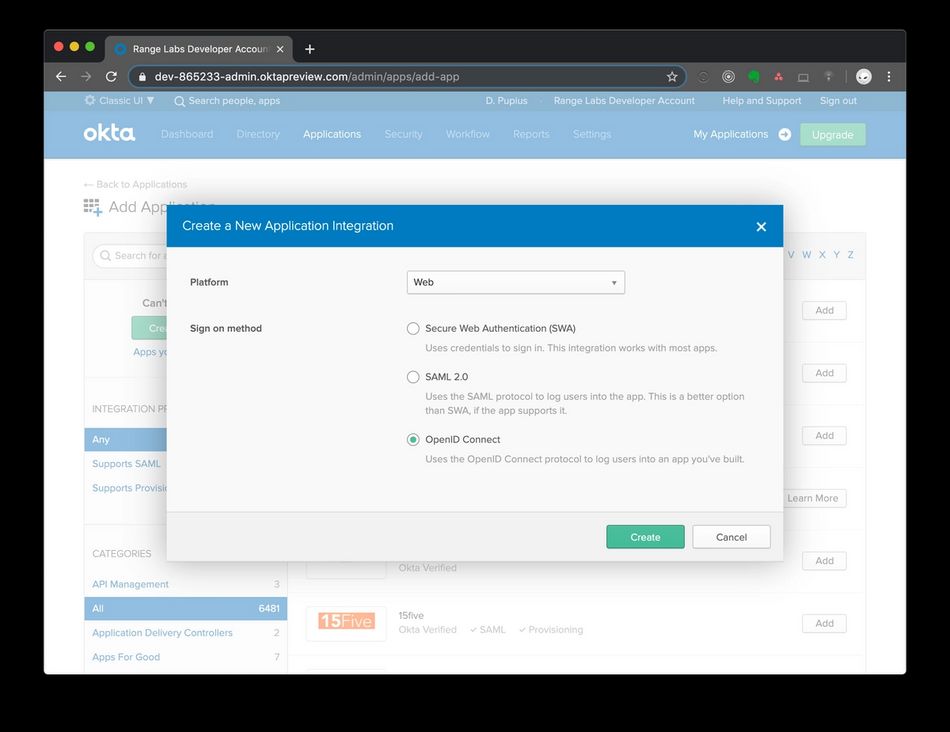
3. Choose "Web" for Platform and "OpenID Connect" for Sign on method. Then "Create".
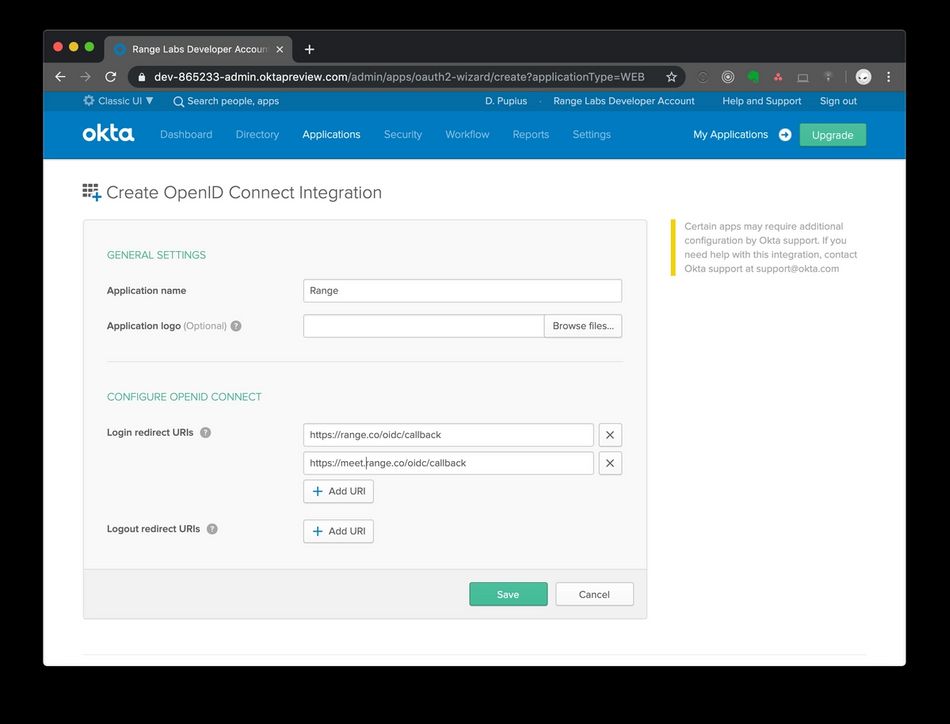
4. In the next screen, set the Application name to "Range" and set Login redirect URIs to https://range.co/oidc/callback and https://meet.range.co/oidc/callback
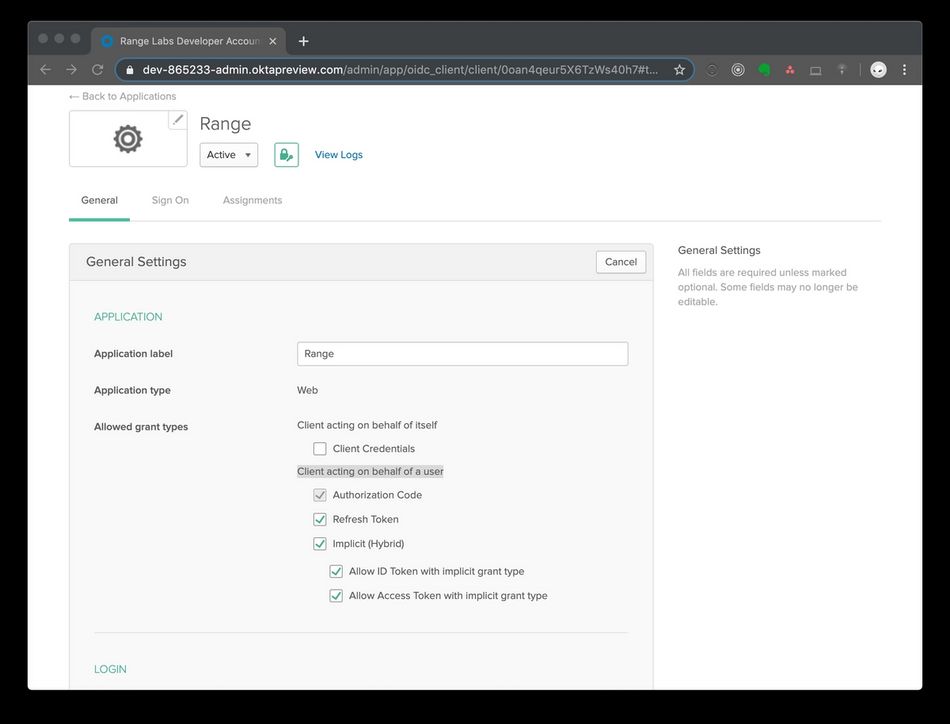
5. Click save, then under General Settings select Edit.
6. For Allowed grant types, check all boxes under Client acting on behalf of a user.
7. Scroll down and set the value for Login initiated by to "Okta or App", check both options for Application visibility, and then update the Initiate login URI to be the URL of your Range workspace. For example, https://range.co/acme-corp. Then press Save.
8. Next make a note of the Client Credentials and send them to support@range.co along with the base URL for your authorization server. This is usually https://{youroktadomain}/oauth2.
If you wish to encrypt the credentials before sending them, you can find our public key on Keybase at https://keybase.io/rangelabs.
9. Once you have received confirmation from the Range team, you are ready to test the integration. You can assigning your own account to the application and try triggering authentication flow from the Okta home screen.
10. If you would like to set the Range app's icon on the Okta dashboard, this one is sized to their requested dimensions: click here.
Still have questions? Reach out to us below.
